| Listing 1 - 10 of 61 | << page >> |
Sort by
|
Book
ISBN: 9781535327435 Year: 2016 Publisher: [s.l.] : Institute for Critical Infrastructure Technology,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
This report covers the primary structure of Chinese espionage initiatives.
Book
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
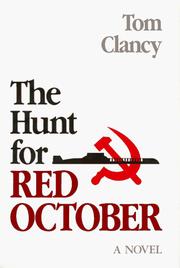
ISBN: 0870212850 Year: 1984 Publisher: Annapolis, MD : Naval Institute Press,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Book
ISBN: 9781138303126 9780429021978 0429021976 9780429664113 0429664117 9780429661396 0429661398 9780429666834 0429666837 Year: 2019 Publisher: Abingdon, Oxon ;New York, NY Routledge
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
This book provides a global introduction to the role of intelligence - a key, but sometimes controversial, aspect of ensuring national security. Separating fact from fiction, the book draws on past examples to explore the use and misuse of intelligence, examine why failures take place and address important ethical issues over its use. Divided into two parts, the book adopts a thematic approach to the topic, guiding the reader through the collection and analysis of information and its use by policymakers, before looking at intelligence sharing. The authors also explore the important associated activities of counterintelligence and the use of covert action, to influence foreign countries and individuals. Topics covered include human and signals intelligence, the Cuban missile crisis, intelligence and Stalin, Trump and the US intelligence community, and the Soviet bloc. This analysis is supplemented by a comprehensive documents section, containing newly released documents, including material from Edward Snowden's leaks of classified material.
INTELLIGENCE SERVICE --- ESPIONAGE --- SPIES
Book
ISBN: 9781440840425 Year: 2019 Publisher: Santa Barbara, CA : Praeger Security International,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
In the post-World War II era, the Soviet Union and the United States wanted to gain an advantage over one another in the international security environment. To do so, both engaged in a variety of intelligence-gathering strategies - some of which involved espionage. This single-volume work provides readers with a comprehensive understanding of the evolution of the espionage game during the Cold War and in the post-Cold War security environment.
ESPIONAGE--USA --- ESPIONAGE--USSR --- ESPIONAGE, AMERICAN--USSR --- ESPIONAGE, SOVIET--USA --- COLD WAR
Book
ISBN: 9782259315975 Year: 2023 Publisher: Paris : Plon
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Book
ISBN: 9781780227849 Year: 2016 Publisher: London : Weidenfeld & Nicolson,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
This is the previously untold - and previously highly classified - story of the melding of technology and espionage. The author's compelling narrative, rich with historical details and characters, takes us from the Second World War to the internet age, with astonishing revelations about espionage carried out today. The computer was born to spy. Under the intense pressure of the Second World War and in the confines of Britain's code-breaking establishment at Bletchley Park, the work of Alan Turing and others led to the birth of electronic espionage. It was a breakthrough that helped win the war. In the following decades, computers transformed espionage from the spy hunting of the Cold War years to the data-driven pursuit of terrorists and the industrial-scale cyber-espionage against corporations in the twenty-first century. Together, computers and spies are shaping the future, and from the rise of China to the phones in our pockets, what was once the preserve of a few intelligence agencies now matters for us all. Drawing on unique access to Western intelligence agencies, on the ground reporting from China and insights into the most powerful technology companies, the author has gathered compelling stories from heads of state, hackers and spies of all stripes. The book is a ground-breaking exploration of the new space in which the worlds of espionage, geopolitics, diplomacy, international business, science and technology collide.
INTERNET IN ESPIONAGE --- ELECTRONIC INTELLIGENCE --- CYBER INTELLIGENCE (COMPUTER SECURITY) --- ESPIONAGE

ISBN: 0861011473 Year: 1983 Publisher: London : Salamander Books,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
MILITARY INTELLIGENCE --- ESPIONAGE --- INTELLIGENCE SERVICE
Book
ISBN: 9780312379223 Year: 2015 Publisher: New York : St. Martin's Press,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
The old world of spying that emphasized the human factor - dead letter boxes, microfilm cameras, and an enemy reporting to the Moscow Center - is history. Or is it ? In recent times, the spymaster's technique has changed with the enemy. He or she now frequently comes from a culture far removed from Western understanding and is part of a less well-organized group. The new enemy is constantly evolving and prepared to kill the innocent. In the face of this new threat, the spymasters of the world replaced human intelligence with an obsession that focuses on the technical methods of spying, ranging from the use of high-definition satellite photography to the global interception of communications. However, this obsession with technology has failed, most spectacularly, with the devastation of the 9/11 attacks. In this modern history of espionage, the author takes us from the CIA's Cold War legends, to the agents who betrayed the IRA, through to the spooks inside Al-Qaeda and ISIS. Techniques and technologies have evolved, but the old motivations for betrayal - patriotism, greed, revenge, compromise - endure. Based on years of research and interviews with hundreds of secret sources, this is an up-to-date expose that shows how spycraft's human factor is once again being used to combat the world's deadliest enemies.
Book
ISBN: 9780140285321 0140285326 Year: 2019 Publisher: London: Penguin books,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
In this book, the first global history of espionage ever written, the author recovers much of the lost intelligence history of the past three millennia - and shows us its relevance.
Espionage --- Secret service --- History --- ESPIONAGE--HISTORY --- SECRET SERVICE--HISTORY --- Espionage - History --- Secret service - History
| Listing 1 - 10 of 61 | << page >> |
Sort by
|

 Search
Search Feedback
Feedback About
About Help
Help News
News