| Listing 1 - 10 of 32 | << page >> |
Sort by
|
ISBN: 9781584885511 1584885513 Year: 2008 Publisher: Boca Raton : Chapman & Hall/CRC,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Cryptography plays a key role in ensuring the privacy and integrity of data and the security of computer networks. Introduction to Modern Cryptography provides a rigorous yet accessible treatment of modern cryptography, with a focus on formal definitions, precise assumptions, and rigorous proofs. The authors introduce the core principles of modern cryptography, including the modern, computational approach to security that overcomes the limitations of perfect secrecy. An extensive treatment of private-key encryption and message authentication follows. The authors also illustrate design principles for block ciphers, such as the Data Encryption Standard (DES) and the Advanced Encryption Standard (AES), and present provably secure constructions of block ciphers from lower-level primitives. The second half of the book focuses on public-key cryptography, beginning with a self-contained introduction to the number theory needed to understand the RSA, Diffie-Hellman, El Gamal, and other cryptosystems. After exploring public-key encryption and digital signatures, the book concludes with a discussion of the random oracle model and its applications. Serving as a textbook, a reference, or for self-study, Introduction to Modern Cryptography presents the necessary tools to fully understand this fascinating subject.
Computer security. --- Cryptography. --- computerbeveiliging --- 005.8 --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Ciphers --- Security systems --- Hacking --- Computerbeveiliging --- Informatiesystemen --- beveiliging --- Computerbeveiliging. --- beveiliging. --- Beveiliging. --- cryptografie --- Computer science --- Computer security --- Cryptography --- Sécurité informatique --- Cryptographie --- Informatiques -- cryptographie = informatics -- cryptography
Periodical
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
cryptanalysis --- secret-key cryptography --- cryptographic protocols --- secure smart system/device --- digital rights management --- quantum safe cryptography --- Data encryption (Computer science) --- Cryptography --- Cryptography. --- Data encoding (Computer science) --- Encryption of data (Computer science) --- Computer security --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Computer Science --- Engineering sciences. Technology
ISBN: 0387965769 3540965769 9780387965765 Year: 1987 Volume: 114 Publisher: New York : Springer-Verlag,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Number theory. --- Cryptography. --- Number Theory --- Nombres, Théorie des --- Théorie des nombres --- Cryptography --- Number theory --- #TELE:SISTA --- 519.72 --- 519.72 Information theory: mathematical aspects --- Information theory: mathematical aspects --- Number study --- Numbers, Theory of --- Algebra --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Data encryption (Computer science) --- cryptografie --- Cryptographie --- Nombres, Théorie des. --- Cryptographie.

ISBN: 0198532873 0198532881 9780198532873 Year: 1988 Publisher: Oxford Clarendon
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Mathematical control systems --- cryptografie --- 519.725 --- Algebraic theory of error-correcting codes --- 519.725 Algebraic theory of error-correcting codes --- Ciphers --- Cryptography --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Data encryption (Computer science) --- Codes --- Contractions --- Abbreviations --- Code names --- Ciphers. --- Cryptography.
Book
ISBN: 0898382718 1461289556 1461316936 9780898382716 Year: 1988 Volume: SECS 52 Publisher: Dordrecht : Kluwer,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Cryptography --- -#TELE:COSIC --- 519.72 --- 519.72 Information theory: mathematical aspects --- Information theory: mathematical aspects --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Data encryption (Computer science) --- Data processing --- #TELE:COSIC --- Mathematical control systems --- cryptologie --- Cryptography. --- Data processing. --- Cryptographie --- Informatique --- Cryptography - Data processing
ISBN: 1139886347 1107100232 110709125X 1107102847 1107094445 1107088224 1107325838 9781107088221 9781107325838 9781107094444 0521398770 9780521398770 9781139886345 9781107100237 9781107102842 Year: 1990 Volume: 154 Publisher: Cambridge : Cambridge University Press,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
In this volume, originally published in 1990, are included papers presented at two meetings; one a workshop on Number Theory and Cryptography, and the other, the annual meeting of the Australian Mathematical Society. Questions in number theory are of military and commercial importance for the security of communication, as they are related to codes and code-breaking. Papers in the volume range from problems in pure mathematics whose study has been intensified by this connection, through interesting theoretical and combinatorial problems which arise in the implementation, to practical questions that come from banking and telecommunications. The contributors are prominent within their field. The whole volume will be an attractive purchase for all number theorists, 'pure' or 'applied'.
Number theory --- Diophantine analysis --- Cryptography --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Data encryption (Computer science) --- Indeterminate analysis --- Forms, Quadratic --- Mathematical models --- #KVIV:BB --- 519.72 --- 519.72 Information theory: mathematical aspects --- Information theory: mathematical aspects --- Mathematical models&delete& --- Congresses --- Mathematical control systems --- cryptografie --- Number theory - Congresses --- Diophantine analysis - Congresses --- Cryptography - Mathematical models - Congresses
ISBN: 9783540259336 9783540403449 3540403442 Year: 2004 Volume: 3000 Publisher: Berlin, Heidelberg : Springer Berlin Heidelberg : Imprint: Springer,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
On August 6, 2002,a paper with the title “PRIMES is in P”, by M. Agrawal, N. Kayal, and N. Saxena, appeared on the website of the Indian Institute of Technology at Kanpur, India. In this paper it was shown that the “primality problem”hasa“deterministic algorithm” that runs in “polynomial time”. Finding out whether a given number n is a prime or not is a problem that was formulated in ancient times, and has caught the interest of mathema- ciansagainandagainfor centuries. Onlyinthe 20thcentury,with theadvent of cryptographic systems that actually used large prime numbers, did it turn out to be of practical importance to be able to distinguish prime numbers and composite numbers of signi?cant size. Readily, algorithms were provided that solved the problem very e?ciently and satisfactorily for all practical purposes, and provably enjoyed a time bound polynomial in the number of digits needed to write down the input number n. The only drawback of these algorithms is that they use “randomization” — that means the computer that carries out the algorithm performs random experiments, and there is a slight chance that the outcome might be wrong, or that the running time might not be polynomial. To ?nd an algorithmthat gets by without rand- ness, solves the problem error-free, and has polynomial running time had been an eminent open problem in complexity theory for decades when the paper by Agrawal, Kayal, and Saxena hit the web.
Number theory. --- Algebra. --- Algorithms. --- Computers. --- Data encryption (Computer science). --- Mathematical statistics. --- Numbers, Prime. --- Polynomials. --- Mathematics --- Statistical inference --- Statistics, Mathematical --- Statistics --- Probabilities --- Sampling (Statistics) --- Data encoding (Computer science) --- Encryption of data (Computer science) --- Computer security --- Cryptography --- Automatic computers --- Automatic data processors --- Computer hardware --- Computing machines (Computers) --- Electronic brains --- Electronic calculating-machines --- Electronic computers --- Hardware, Computer --- Computer systems --- Cybernetics --- Machine theory --- Calculators --- Cyberspace --- Mathematical analysis --- Number study --- Numbers, Theory of --- Algebra --- Prime numbers --- Numbers, Natural --- Algorism --- Arithmetic --- Statistical methods --- Foundations --- Numbers, Prime --- Algorithms --- Computer science. --- Cryptography. --- Computer science --- Number Theory. --- Theory of Computation. --- Cryptology. --- Probability and Statistics in Computer Science. --- Mathematics. --- Informatics --- Science --- Computer mathematics --- Electronic data processing --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Data encryption (Computer science) --- Polynomials --- Polynômes --- Nombres premiers --- Algorithmes --- EPUB-LIV-FT SPRINGER-B

ISBN: 0385495315 Year: 1999 Publisher: New York Doubleday
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Codes have decided the fates of empires, countries, and monarchies throughout recorded history. Mary, Queen of Scots was put to death by her cousin, Queen Elizabeth, for the high crime of treason after spymaster Sir Francis Walsingham cracked the secret code she used to communicate with her conspirators. And thus the course of British history was altered by a few sheets of cryptic prose. This is just one link in humankind's evolutionary chain of secret communication, and just one of the fascinating incidents recounted in The Code Book, written by bestselling author Simon Singh. Combining a superb storyteller's sense of drama and a scientist's appreciation for technical perfection, Singh traces the evolution of secret writing from ancient Greek military espionage to the frontiers of computer science. The result is an epic tale of human ingenuity, with examples that range from the poignant to the peculiar to the world-historical. There is the case of the Beale ciphers, which involves Wild West escapades, a cowboy who amassed a vast fortune, a buried treasure worth $20 million, and a mysterious set of encrypted papers describing its whereabouts--papers that have baffled generations of cryptanalysts and captivated hundreds of treasure hunters. A speedier end to a bloody war was the only reward that could be promised to the Allied code breakers of World Wars I and II, whose selfless contributions altered the course of history; but few of them lived to receive any credit for their top-secret accomplishments. Among the most moving of these stories is that of the World War II British code breaker Alan Turing, who gave up a brilliant career in mathematics to devote himself to the Allied cause, only to end his years punished by the state for his homosexuality, while his heroism was ignored. No less heroic were the Navajo code talkers, who volunteered without hesitation to risk their lives for the Allied forces in the Japanese theater, where they were routinely mistake
Mathematical control systems --- cryptografie --- Cryptography --- Data encryption (Computer science) --- History. --- AA / International- internationaal --- 8 --- 653 --- Filologie. Letterkunde. --- Philologie. Littérature. --- Philology. Literature. --- 8 Filologie. Letterkunde. --- 8 Philologie. Littérature. --- 8 Philology. Literature. --- Handelscorrespondentie : briefwisseling, fax en e-mailverkeer. Telefoon- en telegraafcodes. --- Data encoding (Computer science) --- Encryption of data (Computer science) --- Computer security --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- History --- Handelscorrespondentie : briefwisseling, fax en e-mailverkeer. Telefoon- en telegraafcodes --- Filologie. Letterkunde

ISBN: 1584885084 9781584885085 Year: 2006 Publisher: Boca Raton (Florida) : Chapman & Hall/CRC,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
The third edition of this best-selling text provides unparalleled coverage of the use of cryptographic protocols that establish the steps that must be taken before any type of secret transmission can be completed. The author shows readers how the various parties to the transaction establish their cryptographic identities or keys, covers many of the cryptographic tools used in network security, and discusses topics that include copyright protection techniques and public key infrastructure. Cryptography: Theory and Practice, Third Edition is an outstanding text for senior undergraduate and graduate courses but also a useful reference for professionals interested in network security and cryptographic protocols.
Mathematical control systems --- cryptografie --- Coding theory. --- Cryptography. --- Codage --- Cryptographie --- Cryptography --- 681.3*E3 --- Data encryption: data encryption standard; DES; public key cryptosystems --- 681.3*E3 Data encryption: data encryption standard; DES; public key cryptosystems --- Coding theory --- Data compression (Telecommunication) --- Digital electronics --- Information theory --- Machine theory --- Signal theory (Telecommunication) --- Computer programming --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Data encryption (Computer science) --- Codage. --- Cryptographie.
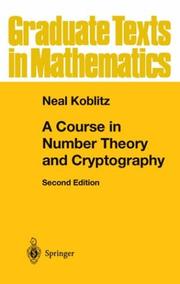
ISBN: 0387942939 1461264421 1441985921 Year: 1994 Volume: 114 Publisher: New York : Springer-Verlag,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Number theory --- 519.72 --- 512.742 --- 511 --- 511 Number theory --- 512.742 Abelian varieties and schemes. Elliptic curves --- Abelian varieties and schemes. Elliptic curves --- 519.72 Information theory: mathematical aspects --- Information theory: mathematical aspects --- Number study --- Numbers, Theory of --- Algebra --- Cryptography --- Cryptanalysis --- Cryptology --- Secret writing --- Steganography --- Signs and symbols --- Symbolism --- Writing --- Ciphers --- Data encryption (Computer science) --- cryptografie --- Cryptography. --- Cryptographie --- Théorie des nombres --- Number theory.
| Listing 1 - 10 of 32 | << page >> |
Sort by
|

 Search
Search Feedback
Feedback About
About Help
Help News
News